You're probably in one of two places right now. You have a strong idea for a digital product in care delivery, remote monitoring, insurance workflow, or patient engagement, and you want to build it before the window closes. Or you already have a first version, and you've realised that getting a Canadian healthtech platform into production is less about shipping screens and more about surviving compliance, integration, and procurement.
That's where many first major builds go sideways. A founder starts with a patient app. A clinic group starts with scheduling and virtual care. An insurer starts with claims automation tied to clinical records. Then the actual constraints show up. Where does the data live? Which provincial rules apply? Can your platform exchange data with an existing EMR without corrupting records? Who gets access to what, and how do you prove it later?
Healthtech platform development in Canada rewards teams that treat architecture as a business decision, not just a technical one. If your foundation is wrong, every later step costs more. If your compliance model is borrowed from a U.S. HIPAA playbook, you can end up with a platform that looks polished but stalls in Canadian deployment.
Navigating the Healthtech Opportunity in Canada
A Vancouver clinic group rolls out online booking and virtual visits. Within months, patients ask for digital intake, clinicians want fewer manual handoffs, and management wants reporting that stands up to payer and procurement scrutiny. A Montreal startup starts with remote monitoring, then learns its buyers also expect consent tracking, bilingual workflows, and clean integration paths into existing clinical systems. In both cases, the opportunity is larger than the first feature set, but so is the build.
Canada gives healthtech founders and care operators real room to grow. Public systems are under pressure, private clinics are modernising patient access, and care delivery keeps shifting toward hybrid models that combine in-person, virtual, and home-based services. Investment has followed that shift. CB Insights' State of Digital Health 2024 report tracks continued funding into platform-based digital health categories, and Statista's Digital Health Canada outlook points to sustained market growth across telemedicine, digital treatment, and connected care. The practical takeaway is simple. Buyers are not looking for another standalone tool if it creates more fragmentation.
Why Platform Thinking Matters
In Canada, a healthtech platform usually has to serve more than one constituency from the start. Patients need access and clarity. Clinicians need speed and low-friction workflows. Operators need reporting, permissions, and defensible records. If one of those groups is ignored, adoption slows down fast.
That is why platform decisions show up earlier than many founders expect.
A clinic may start with scheduling and intake, then need secure messaging, document exchange, and role-based staff access. A startup may launch remote monitoring first, then get pushed toward insurer reporting, care team alerts, and EMR data exchange. If the first version is built as a narrow product with brittle APIs, weak identity design, or no clear data boundaries, every expansion costs more in both engineering time and compliance review.
Practical rule: Build for the second workflow while launching the first.
That does not mean adding every enterprise feature to an MVP. It means choosing a data model, permission structure, and integration pattern that can survive the next sales conversation. For teams working through early architecture and privacy requirements, this healthcare compliance software development guide is a useful reference point.
What Founders and Clinic Owners Often Underestimate
The hardest part is rarely the interface. It is operational fit.
Canadian buyers tend to test a platform against their existing environment, not against the founder's product vision. A hospital-affiliated clinic will ask how the system handles local privacy obligations, auditability, and user provisioning. A private practice will focus on staff time, patient drop-off, and whether the platform reduces phone calls instead of creating new admin work. An insurer or enterprise partner will look for reporting discipline, access controls, and predictable integration scope.
Three realities shape early outcomes:
Compliance scope changes the architecture early. Consent handling, retention rules, and provincial expectations affect how you structure records, logs, and cloud environments.
Integration work drives timelines. EMRs, lab systems, scheduling tools, and payer workflows add dependencies that cannot be treated as cleanup work after launch.
Clinical friction kills adoption. If a nurse has to click through four extra screens or re-enter data already captured elsewhere, the feature will stall no matter how polished the demo looks.
A development partner can influence outcomes more than founders expect at this stage. Good teams do not just ship features. They help define what belongs in version one, what should wait, and where a shortcut will create an expensive compliance or rework problem six months later.
The Canadian opportunity is strong, but it rewards teams that design for procurement, care delivery, and privacy reality at the same time.
The Canadian Regulatory Gauntlet Demystified
A Toronto clinic signs off on your pilot. Then procurement asks three questions your product team has not settled: where patient data will live, how consent is recorded, and what an audit trail looks like when a staff member opens a chart after hours. That is often the moment a promising build slows down in Canada.

What the Rules Mean in Practice
Canadian healthtech products operate under overlapping privacy obligations. PIPEDA applies to personal information in commercial activity at the federal level, but healthcare delivery is also shaped by provincial statutes and regulators. In Ontario, teams usually run into PHIPA first. Alberta has HIA. British Columbia has PIPA and public-sector rules under FIPPA. Quebec has its own privacy regime with stricter consent and governance expectations than many founders expect.
The practical effect is simple. Compliance decisions shape product decisions early.
A founder or clinic operator usually needs answers in four areas:
Data location and vendor choice. If you host outside Canada or use third-party sub-processors without clear controls, privacy review gets harder fast. Some buyers will stop there.
Consent records and secondary use. You need a defensible record of what the patient agreed to, what the organisation is allowed to do without fresh consent, and how that changes by workflow.
Role-based and context-based access. A receptionist, nurse, physician, billing admin, and support contractor should not see the same information set.
Audit and breach handling. Logs must show who accessed what, when, from where, and whether the action matched policy. If an incident happens, your team needs a process, not a scramble.
I have seen teams treat these as policy work for later. That usually leads to expensive rework in the data model, permission system, and admin tooling.
Why Canada-Specific Guidance Matters
Many early healthtech builds in Canada borrow assumptions from HIPAA-focused products. That creates gaps. HIPAA familiarity does not answer Canadian questions about provincial custody rules, cross-border service providers, or the procurement language a hospital network will put in front of you.
Canadian buyers also expect interoperability decisions to line up with privacy controls. If your team is still defining APIs, identity boundaries, or data exchange formats, review the standards for health information systems alongside your privacy requirements, not after them. Integration choices affect what data leaves your platform, how it is mapped, and what evidence you can produce during an assessment.
The broader pattern is clear from procurement and implementation work across the market. Buyers are asking harder questions, earlier in the cycle. They want to know whether your platform can support Canadian hosting, produce usable audit records, and separate permissions cleanly across clinics, practitioners, and admins. Strong governance is now part of product viability, not a legal add-on.
The Questions Your Team Should Answer Before Design Begins
Before design starts, get specific. General statements like "we use secure cloud" or "consent is handled in the app" will not hold up in diligence.
Which laws and regulators apply to each customer type? A private clinic, insurer, virtual care provider, and hospital-affiliated group can trigger different review paths.
Where will production data, backups, analytics data, and logs be stored? Include every vendor in that answer.
What is your legal basis for each data flow? Separate direct care, operations, billing, analytics, and product improvement.
How are permissions granted, changed, and removed? Account provisioning is often a bigger risk than the login itself.
What audit evidence can you show on demand? If a clinic asks who viewed a record last Tuesday, you should be able to answer without engineering work.
What is your incident process? Name the trigger, internal owner, investigation path, notification steps, and retention of evidence.
Teams that need a more detailed view of privacy obligations, auditability, and secure delivery in regulated software can use this guide on healthcare compliance software development as supporting reading.
Architecting a Compliant and Scalable Platform
A clinic in Ontario signs a pilot agreement, then asks two questions that reshape the build. Will patient data stay in Canada, and can the platform prove who changed a chart, consent record, or appointment workflow? If your architecture cannot answer both on day one, the rebuild starts earlier than founders expect.
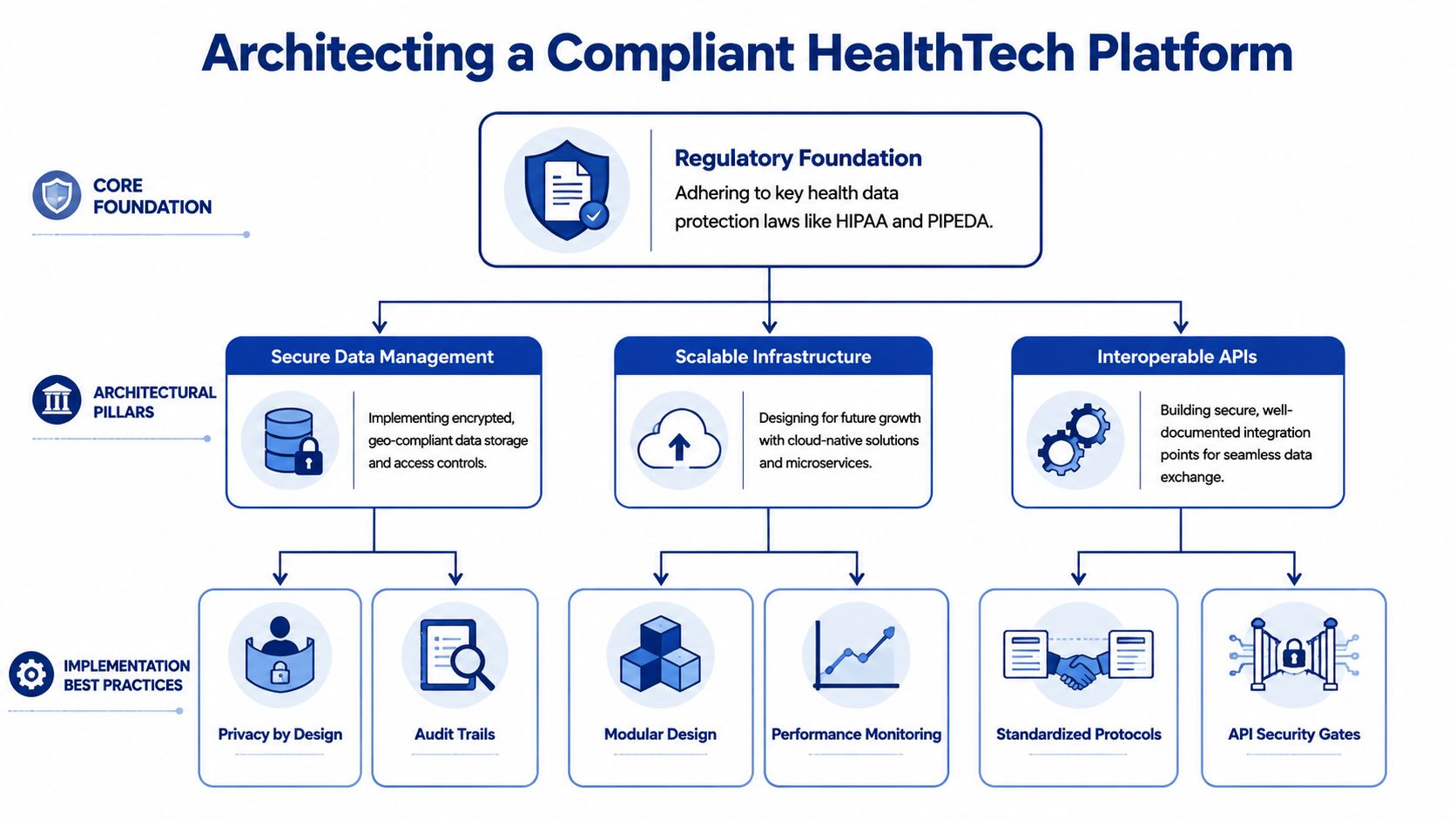
Start With the Foundation
For Canadian healthtech platform development, architecture starts with jurisdiction, not tooling. PIPEDA sets the federal privacy baseline for many commercial activities, but provincial health privacy statutes and public-sector rules often drive stricter operational decisions. In practice, that affects where production systems run, how support access is controlled, what metadata is retained, and which vendors belong in the stack.
A workable foundation usually includes:
Canadian hosting for regulated workloads, such as Azure Canada Central or AWS Canada regions, with a documented reason if any service sits outside Canada
Separate trust zones for public APIs, internal admin tools, integration services, and back-office operations
Hard separation across dev, staging, and production, including separate credentials and masked or synthetic test data
Infrastructure as code, so changes are reviewed, repeatable, and tied to tickets and approvals
Centralised audit design from the start, because clinics will ask for evidence, not architecture diagrams
Founders often ask whether they need a monolith or microservices. The honest answer is that an early monolith is often cheaper to ship and easier to secure if one team owns it well. A modular monolith with clear domain boundaries usually beats a rushed microservices build. Split services only when team structure, scaling patterns, or regulatory separation make the extra operational cost worth paying.
Design Interoperability Into the Core Model
Interoperability work should shape the core data model, not sit at the edge as a connector project. Canadian teams run into a predictable problem here. Product decisions are made around UI flows, then integration starts later, and every external connection needs custom mapping for patient identity, encounters, documents, and provider records.
That cost compounds quickly.
The better approach is to pick a canonical clinical model early and force internal services to respect it. If FHIR is your exchange contract, use it deliberately. Keep internal extensions controlled. Decide where HL7 v2 translation happens. Define how provincial identifiers, practitioner identifiers, and consent artefacts are represented before the first integration goes live.
Practical choices usually look like this:
Use FHIR R4 as the primary external contract where partner systems can support it.
Keep an integration layer for HL7 v2 and file-based interfaces, because many Canadian provider environments still depend on them.
Treat patient identity resolution as its own architectural concern, especially when clinics, practitioners, and external labs all create overlapping records.
Version mappings and interface rules, because integration failures are often caused by silent field changes rather than full API outages.
If your team needs a business-level reference point, this overview of standards for health information systems is useful. For implementation details, this guide to API integration in healthcare digital ecosystems is closer to the work engineering teams have to deliver.
A simple test helps here. If onboarding one new EMR requires logic changes in the frontend, backend, reporting jobs, and analytics pipeline, the platform does not yet have a stable interoperability layer.
Build Around Bounded Domains
Canadian health platforms usually fail at scale for one of two reasons. They either put too much logic into one shared database schema, or they split too early into services without clear ownership. Both create expensive integration debt.
Clearly bounded domains reduce that risk. Common domains include patient identity, scheduling, clinical documentation, messaging, billing, reporting, and consent. Consent deserves special attention in Canada because legal and operational expectations differ by province and by care setting. Treating it as a checkbox on the user table causes trouble later.
A practical early-stage structure looks like this:
| Layer | What it should do |
|---|---|
| Experience layer | Patient portal, clinician dashboard, admin console, partner interfaces |
| Application layer | Workflow orchestration, business rules, validation, notifications |
| Interoperability layer | FHIR APIs, HL7 translation, webhook handling, integration queues |
| Data layer | Clinical records, operational data, audit logs, consent records |
| Security layer | Identity, access policy enforcement, encryption, and monitoring |
This model gives teams a place to put change. Scheduling rules change. Billing rules change. Provincial data-sharing requirements change. If every change lands in one shared service, release speed drops and regression risk rises.
I also recommend separating operational analytics from the clinical transaction path early. Product teams want dashboards fast. Clinics want the core record to remain accurate and traceable. Those goals align better when reporting pipelines read from controlled events or replicas instead of competing with live clinical writes.
What Holds Up Under Real Use
The platforms that last are usually less flashy than the demo. They have a single source of truth for patient identity, documented service contracts, readable audit events, and integration patterns that survive staff turnover.
The ones that struggle are predictable:
HIPAA-first assumptions applied to Canadian customers
Province-specific requirements are handled through a manual process instead of a system design
Custom integrations with no canonical model
Permissions embedded in code instead of policy and role structures
Shared data stores with weak domain ownership
Reporting and product analytics writing back into regulated records
Good architecture lowers compliance costs later. It also lowers delivery cost, because the second clinic, the first hospital pilot, and the first insurer integration stop forcing a redesign each time.
Fortifying Your Platform With Ironclad Security
A common failure pattern looks like this. A clinic rolls out online booking, secure messaging, and a patient portal. Six months later, a staff member exports more data than their role requires, a vendor integration logs PHI in the wrong place, and nobody can reconstruct the full access trail without pulling records from three systems. In Canada, that problem is not just technical debt. It can trigger breach reporting, regulator scrutiny, contract risk with provider partners, and expensive remediation under PIPEDA and provincial health privacy rules such as Ontario's PHIPA and Alberta's HIA.

Security architecture decides whether your platform contains that kind of incident or spreads it. For Canadian healthtech platforms, I advise founders to start with Zero Trust and assume every request must earn access through identity, policy, and context. Hospital networks, remote staff, contractors, patients, and third-party apps all touch the system from different environments. A VPN and a corporate domain are not enough.
The Office of the Privacy Commissioner of Canada has published findings on safeguards, breach handling, and accountability under PIPEDA, and Ontario's Information and Privacy Commissioner has issued decisions and guidance under PHIPA that make one point clear. You need controls that stand up in an investigation, not just controls that look good in a sales deck. That means designing for least privilege, auditability, and breach containment from the first production release.
Security Controls That Hold Up in Real Operations
Founders often ask where to spend first. My answer is consistent.
Encrypt PHI at rest and in transit. Use managed key services where possible, separate key access from application access, and apply transport encryption across APIs, admin tools, internal services, backups, and queued jobs.
Build identity around roles, attributes, and session context. Basic RBAC helps, but Canadian clinic workflows usually need more. Access often depends on province, care team, site, employment status, patient relationship, and task.
Keep an audit trail that a privacy officer can use. Log record access, edits, exports, sharing events, admin changes, failed logins, permission grants, and API activity. Make logs tamper-evident and searchable.
Treat APIs as regulated entry points. Every endpoint needs authentication, authorisation, input validation, rate limiting, and clear rules for what gets logged.
Separate privileged workflows from day-to-day use. Admin tooling, support access, and database operations should run through tighter controls than standard clinical actions.
A good design also limits blast radius. Segment environments. Isolate tenants or clinic groups where the business model allows it. Keep production data out of test systems. Put strict controls around support access, because support shortcuts are a common source of privacy exposure.
What Usually Gets Missed
Teams new to healthcare spend time on encryption and MFA, then underinvest in operational discipline. The bigger risks often sit in ordinary workflows. CSV exports sent to the wrong endpoint. Long-lived service credentials shared between vendors. Internal dashboards with broader access than the clinical app. Backups are restored and tested for availability, but not for privacy controls.
I have seen Canadian projects pass a feature review and still fail a partner security review because they could not answer basic questions: Who can impersonate a clinic user? How is emergency access approved and logged? Can a revoked contractor token still call background APIs? Which province stores which category of patient data?
Those are architecture questions, not paperwork questions.
Build Security Into Delivery, Not Just Production
Security needs to be part of how code ships.
A workable baseline includes MFA for all privileged accounts, short-lived credentials, secrets management outside source control, dependency and container scanning in CI/CD, infrastructure change review, and alerting on unusual access patterns. Penetration testing matters too, but it should confirm your controls, not replace them. For teams tightening their engineering process, this guide to secure healthcare software development is a useful reference alongside your threat model and release checklist.
The partner and buyer side matters as much as the engineering side. Clinics, hospitals, and insurers will ask for security questionnaires, incident response procedures, data residency details, and evidence of access control design. If your team needs broader context on information-system risk, the overview on how to secure health care with Vulnsy is a useful companion read.
A practical test is simple. If a privacy regulator, a hospital security lead, and your own incident team each asked who accessed a patient record, why they had access, what they changed, and whether the event crossed a provincial boundary, your platform should answer in minutes, not days.
From MVP Strategy to Full-Scale Launch
An MVP in healthcare is often misunderstood. It doesn't mean “bare minimum features, and we'll worry about the hard stuff later.” In healthtech platform development, viable means safe enough to use, compliant enough to sell, and structured enough to extend.
What a Real Healthcare MVP Includes
A proper first release usually has fewer workflows than founders want and more non-functional requirements than they expect. That's normal.
For example, a clinic platform MVP might include patient registration, appointment booking, secure messaging, clinician notes, and audit logging. It might exclude advanced analytics, insurer-facing automation, or broad partner integrations until the core workflow is stable. A remote care product might launch with one condition pathway and one device integration instead of trying to support every speciality at once.
The point is focus. If the MVP can't handle one clinical workflow cleanly, adding more features just increases the blast radius.
Use Phased Rollout, Not Big-Bang Launch
The safest path is usually staged.
Phase one should prove the workflow with a narrow user group. That might be one clinic, one care team, or one internal operations unit. You want to validate how staff use the product in practice, not how they describe using it in discovery calls.
Phase two should harden the platform around the issues that only live usage reveals. Permission gaps, slow intake forms, duplicate records, missing notifications, and confusing error states show up quickly in healthcare.
Phase three is where a broader scale becomes reasonable. Only then should you widen integrations, expand geography, or add adjacent modules.
A rollout model that works well in practice often includes:
Controlled pilot group with real users and bounded scope
Production-like staging for final validation of workflows and data handling
Clinical acceptance testing with people who own the process, not just software testers
Security validation before expansion to more sites or partners
Measured enablement for staff training, support, and escalation
Launch advice: If clinicians need a workshop to understand your core workflow, the product isn't ready. Training should explain policy and edge cases, not rescue poor design.
Agile Still Works in Healthcare, With One Adjustment
I'm strongly in favour of agile delivery for healthtech, but it has to be disciplined. Fast iteration is useful only when the team respects fixed constraints around privacy, security, and data quality.
That means each sprint should include more than feature work. You need a privacy review for new data collection, an access review for new roles, an integration review for new data flows, and test evidence for critical workflows. Teams that skip those checks in the name of speed usually create hidden debt that blocks launch later.
A practical agile model in healthtech tends to work like this:
| Delivery area | What to keep non-negotiable |
|---|---|
| Product design | Clinical workflow review, consent visibility, accessibility |
| Engineering | Secure coding, API versioning, event logging |
| QA | Functional testing plus edge-case workflow testing |
| Security | Auth checks, permission checks, vulnerability review |
| Release | Rollback plan, support plan, and incident ownership |
Test the Product the Way Care Is Actually Delivered
Standard QA won't catch enough. A feature may pass every ticket and still fail in a clinic because the sequence is wrong, the terminology is off, or the timing doesn't fit the workday.
So test in context:
Front-desk staff should run intake and scheduling.
Clinicians should document, review, and sign off in realistic scenarios.
Administrators should test permissions, exports, and audit visibility.
Patients should complete common tasks on ordinary devices, not just polished demos.
The best launch plans respect one principle. Healthcare software is successful when it reduces friction without reducing control.
Making Smart Decisions on Costs and Resources
This is usually the point where founders ask the practical question they wanted answered from the start. Who should build this, and what kind of spending pattern makes sense?
There isn't one correct model. The right choice depends on your internal product leadership, compliance maturity, technical complexity, and how quickly you need to move. What matters is understanding the trade-offs clearly.
Where Costs Actually Come From
For a healthtech platform, cost isn't just development time. It spreads across several categories:
Discovery and architecture for workflow design, compliance interpretation, and system planning
Product design for patient, clinician, and admin experiences
Engineering across front-end, back-end, integration, and DevOps
Security and compliance work, such as access design, audit readiness, and policy implementation
Infrastructure and support after launch
Ongoing maintenance as regulations, integrations, and workflows change
For mobile-first founders, it also helps to understand how consumer-facing app decisions affect budget and scope. This guide on planning mobile app investment is useful because it highlights how feature choices and team structure change total spend, even before healthcare-specific requirements are layered on.
Healthtech Development Resourcing Models Compared
| Criteria | In-House Team | Full Outsourcing | Team Augmentation |
|---|---|---|---|
| Control over roadmap | Highest control. Product decisions stay internal. | Lower day-to-day control unless governance is strong. | High control if internal product leadership is active. |
| Speed to start | Usually slower because hiring takes time. | Fast if the vendor already has delivery capacity. | Faster than in-house when you need specific roles quickly. |
| Compliance experience | Depends on who you hire. Hard to build from scratch. | It can be strong if the vendor knows Canadian healthcare. | Let's you add targeted expertise in compliance and integration. |
| Institutional knowledge | Strong over time if retention is good. | Risk of knowledge living outside your organisation. | Better balance if external specialists work inside your process. |
| Flexibility | Harder to resize quickly. | Easier to scale up or down contractually. | Good for filling gaps without rebuilding the whole team. |
| Upfront management burden | High. You own the hiring process and oversight. | Lower internally, but vendor management becomes critical. | Moderate. Internal leadership still matters. |
| Best fit | Organisations with long runways and strong internal leadership | Teams that need an end-to-end build partner | Startups and clinics that need speed plus retained product ownership |
How To Choose Without Overcomplicating It
If you have a seasoned CTO, a product owner who understands clinical workflow, and time to recruit carefully, in-house can work well. If you need to move quickly and lack depth in healthcare engineering, full outsourcing can make sense, but only if the vendor understands Canadian compliance and interoperability.
Team augmentation is often the most practical middle ground for growing healthtech teams. You keep product control, but add the specialists you don't yet have, such as FHIR integration engineers, security architects, or senior platform developers. That model is often easier on operational risk because you're not handing over the entire product brain.
A good resourcing decision isn't about minimising invoices. It's about avoiding expensive mistakes in architecture, compliance, and launch sequencing.
The Future of Healthtech and Your Next Steps
The next wave of Canadian healthtech won't be defined by prettier portals. It will be defined by systems that can combine secure data exchange, workflow automation, AI support, and connected devices without collapsing under compliance pressure.
AI-driven triage, remote monitoring, and insurer-provider coordination all depend on the same basics. Clean data. Clear permissions. Reliable audit trails. Interoperable APIs. If those pieces are weak, the advanced features become liabilities instead of advantages.
That's why future-proofing doesn't start with AI tooling. It starts with sound platform design. An IoMT-ready product still needs identity controls. An AI-assisted clinical workflow still needs traceable data lineage and human review points. A multi-province rollout still needs architecture that respects jurisdictional differences.
A Practical Checklist Before You Build Further
Use this as a working filter for your next decision:
Define the narrowest high-value workflow first. Don't launch broadly if one care path still breaks.
Confirm Canadian compliance assumptions early. Don't let HIPAA-era defaults shape your platform.
Choose infrastructure that supports residency and auditability. Hosting is a product decision in healthcare.
Adopt interoperability standards deliberately. FHIR planning belongs in architecture, not just in integration tickets.
Set Zero Trust as the baseline. Access should be earned, constrained, and logged.
Launch in phases. Real users expose design flaws faster than internal demos do.
Match your team model to risk. The cheapest build path can become the most expensive correction later.
What To Do Next
If you're still at the concept stage, start with architecture and regulatory mapping before feature scoping gets too detailed. If you already have a prototype, review it for residency, access control, and interoperability assumptions before adding more functionality. If you're preparing to sell to clinics, hospitals, or insurers, tighten the parts buyers scrutinise most closely: data handling, audit evidence, and integration readiness.
Healthtech platform development in Canada is demanding, but it's not opaque. The teams that do well treat compliance as design input, interoperability as a product capability, and security as an operating discipline. When those three are present, growth becomes much easier to support.
If you're planning a Canadian healthtech platform and want a practical review of architecture, interoperability, or compliance choices before you commit to a build path, Cleffex Digital Ltd can help assess the scope, identify risk areas, and support delivery with custom software development and agile engineering for regulated healthcare products.