Your clinic probably still gets the job done. Patients are seen, claims are processed, referrals eventually move, and staff know which screens to avoid because they freeze at the wrong moment. That’s exactly why legacy platforms survive so long in healthcare. They’re frustrating, but familiar.
The problem is that familiar systems age badly in care settings. A slow patient portal becomes a front-desk burden. A disconnected billing module creates rework. An old on-premise application makes every change feel risky because nobody wants to break scheduling, charting, or reporting in the middle of a busy week. By the time leadership starts looking at healthcare platform modernisation services, the issue usually isn’t “should we modernise?” It’s “how do we modernise without disrupting care, violating Canadian privacy rules, or blowing the budget?”
In Canada, that question has extra weight. You’re not only dealing with old software. You’re dealing with provincial privacy obligations, fragmented interoperability, and funding realities that look very different from the US market most articles are written for. A practical modernisation plan has to fit those constraints from day one.
Why Your Legacy Healthcare Platform Is a Ticking Clock
A typical warning sign looks ordinary at first. Staff enter patient information into one system, then copy parts of it into another. Lab updates arrive, but they don’t flow cleanly into the record clinicians use every day. A patient asks for online access, digital intake, or faster follow-up, and the answer is still a workaround.
That’s not just an IT nuisance. It’s an operational drag that touches booking, triage, charting, privacy management, reporting, and patient satisfaction. Legacy platforms rarely fail in one dramatic event. They create constant friction, and that friction gets expensive.
Modernisation Is a Business Decision First
When healthcare leaders hear “modernisation,” they often picture a technical rewrite. In practice, healthcare platform modernisation services are about making care delivery and administration more resilient. The technology matters, but the business outcome matters more.
A sound modernisation effort should help you:
Reduce manual handoffs, so staff stop re-entering the same data across systems
Improve patient access through better portals, booking flows, and communication tools
Lower operational risk by replacing brittle integrations and unsupported infrastructure
Prepare for interoperability so your systems can exchange information more reliably
Support future services such as telehealth, remote monitoring, analytics, or AI-enabled workflows
Practical rule: If your modernisation plan starts with tools and ends with workflow impact, it’s backwards. Start with workflow failures, then choose the architecture that fixes them.
What Pushes Canadian Providers To Act
Four pressures usually force the issue.
First, patients expect digital access that feels normal. They won’t describe it as modernisation, but they feel the gap immediately when booking is clunky, intake is paper-heavy, or records are trapped behind phone calls and fax-driven workarounds.
Second, security risk grows faster than most old systems can adapt. Many legacy applications were built for a closed environment. Modern healthcare operations aren’t closed. They involve remote access, third-party vendors, cloud services, and increasing scrutiny over how data is stored and audited.
Third, interoperability has become a daily operational need, not a future ambition. Canadian providers have to work across provincial realities, older data structures, and differing standards. If your platform can’t exchange data cleanly, every new partnership becomes a custom project.
What Doesn’t Work
The wrong response is to keep patching around the same structural issues. Teams add one more interface, one more script, one more spreadsheet, one more manual check. That can postpone replacement, but it doesn’t create a durable platform.
The other mistake is waiting for the “perfect time.” In healthcare, there usually isn’t one. There’s only a point where the cost of doing nothing becomes harder to hide than the cost of change.
Core Strategies for Platform Modernisation
Modernisation choices are easier to understand if you think of the platform like a vehicle your organisation depends on every day. Sometimes you move it to a better garage. Sometimes you replace the engine. Sometimes you redesign core components. And sometimes the vehicle is so outdated that keeping it on the road costs more than changing direction.
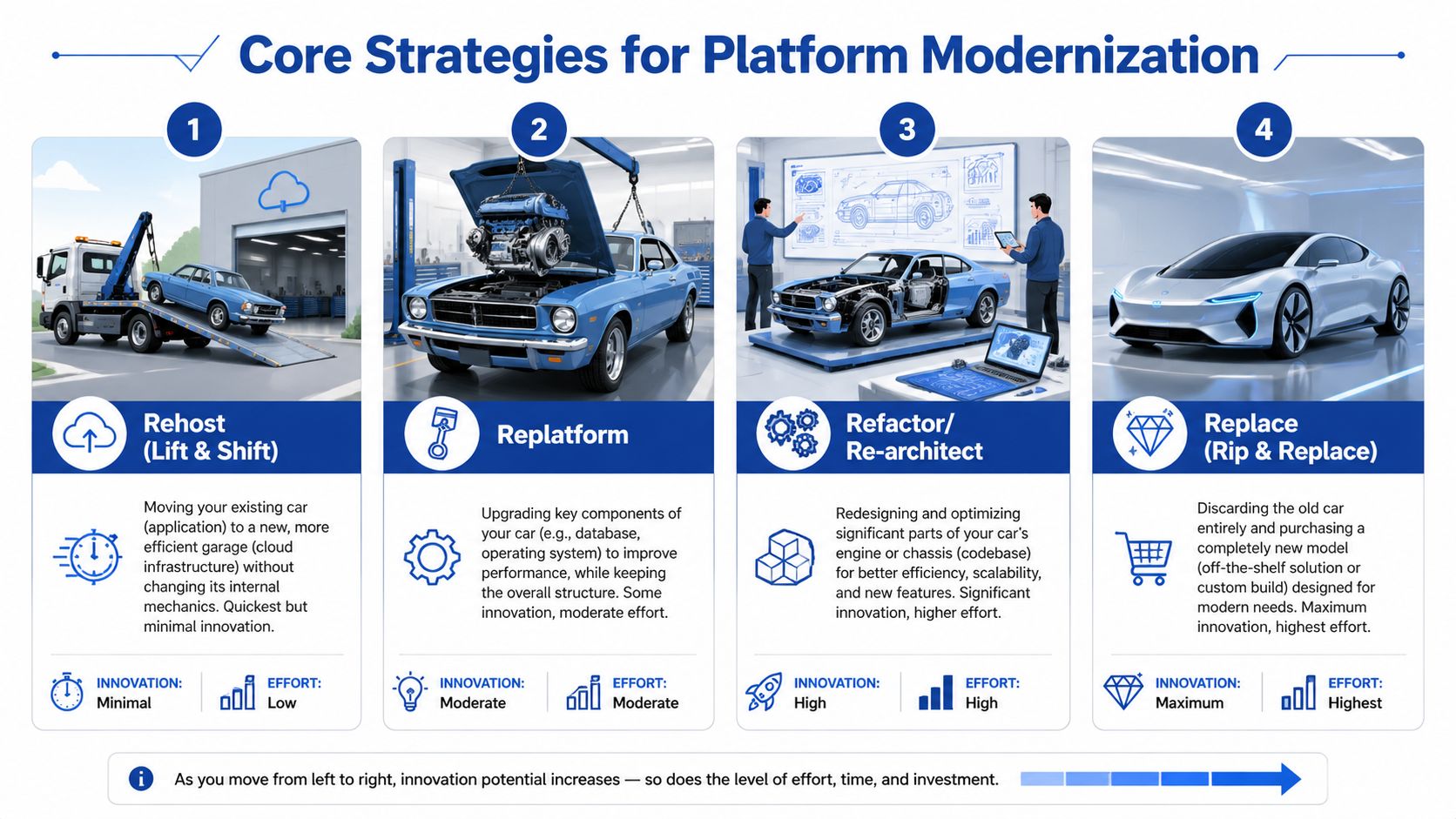
The right strategy depends on what’s broken, what must stay stable, and how much change your staff can absorb at once. If you need a broader planning lens, this guide to enterprise application modernisation strategy is a useful reference for aligning technical choices with business priorities.
Four Common Paths
| Strategy | What it means | Best fit | Main trade-off |
|---|---|---|---|
| Rehost | Move the existing application to a newer infrastructure with minimal code change | Systems that still function but sit on fragile hardware | Fastest move, but limited improvement |
| Replatform | Keep the core app, upgrade key components such as database or runtime | Platforms with stable business logic but ageing dependencies | Moderate effort, moderate gain |
| Rearchitect | Redesign major parts of the application for flexibility and scale | Systems that must support new workflows, integrations, or products | Higher cost and delivery risk |
| Replace | Retire the old system and adopt a new product or new custom build | Platforms that no longer fit clinical or operational needs | Biggest change burden |
Where Each One Works
Rehosting is useful when infrastructure is the immediate problem. If your application runs acceptably but the hosting environment is hard to secure, hard to back up, or expensive to maintain, lift-and-shift can buy time. It won’t fix poor user experience or bad data design, but it can reduce technical fragility.
Replatforming goes a step further. You keep the application shape, yet improve important layers underneath it. This is often the sensible middle ground for providers that need better performance or manageability without forcing clinicians and administrators through a completely new system.
Replatform if the workflow still makes sense, but the plumbing doesn’t.
Rearchitecting is for platforms that need to behave differently, not just run on newer servers. If you want cleaner APIs, modular services, better auditability, or easier rollout of new patient-facing features, this is often where you end up. It’s more disruptive, so it needs tighter scope control.
Replacement makes sense when the current platform is no longer strategically defensible. The danger is assuming a new product automatically means a better operating model. In healthcare, replacement projects fail when organisations underestimate data migration, workflow redesign, training, and integration effort.
The Pattern That Often Works Best
For many Canadian providers, the safest route is incremental replacement using a strangler approach. You keep the core system running while surrounding it with newer services. A modern booking layer, integration layer, or patient communication module takes over one function at a time until the legacy core becomes smaller and easier to retire.
This approach works particularly well in care environments because it limits operational shock. Front-desk teams, clinicians, and finance staff don’t have to relearn everything at once.
It also aligns with how platform teams are evolving. The broader future of DevOps with IDPs is relevant here because modernisation increasingly depends on internal platforms that standardise deployment, security, and developer workflows instead of relying on one-off engineering heroics.
What Usually Fails
Three choices repeatedly create trouble:
Big-bang replacement without process redesign leads to expensive disappointment
Pure lift-and-shift, sold as a transformation, leaves the same problems in a different environment
Architecture-first programmes with no operational owner create elegant diagrams and weak adoption
The strongest modernisation strategy is rarely the most dramatic one. It’s the one your organisation can govern, fund, and absorb while still delivering care every day.
The Technology Stack of a Modern Health Platform
A modern health platform doesn’t need every fashionable tool. It needs a stack that makes change safer, data exchange cleaner, and operations easier to manage. Most executives don’t need low-level engineering detail. They need to know which building blocks matter and why.
Cloud Gives You Operating Flexibility
Cloud infrastructure matters because healthcare demand is uneven, integrations keep growing, and disaster recovery can’t rely on hope. In a modern setup, infrastructure becomes easier to scale, patch, monitor, and recover.
That doesn’t mean every workload belongs in a public cloud. Many Canadian providers land on a hybrid model, where sensitive or hard-to-move systems remain partly anchored while newer services run in cloud environments built for resilience and faster release cycles. The point isn’t to “move everything.” It’s to stop treating servers as the main constraint on service design.
If your team is evaluating hosting choices in a Canadian context, this overview of cloud-based healthcare software in Canada is a practical place to compare deployment considerations.
APIs Make Disconnected Systems Usable
An API is the controlled handshake between systems. In healthcare, that means your EHR, billing platform, patient portal, scheduling tool, telehealth service, and analytics environment can exchange data without relying on brittle file transfers or manual duplication.
APIs matter because they reduce dependency on custom point-to-point integrations. They also make vendor changes less painful. If you build clean interfaces now, you won’t have to rebuild the entire estate each time one application changes.
For teams planning integration-heavy projects, this resource on how to implement seamless healthcare data exchange is useful for thinking through interoperability patterns beyond basic messaging.
Microservices Support Targeted Change
A monolith forces your team to treat every update like a full-platform risk. Microservices separate capabilities into smaller deployable units. That can include appointments, notifications, identity, billing rules, referral intake, or reporting.
That doesn’t mean every platform should be chopped into dozens of services. Overdoing microservices creates management overhead. The practical gain comes from isolating high-change or high-value functions so teams can improve them without destabilising everything else.
A good rule is simple:
Use modular services for areas that change often
Keep stable domains simple if they don’t need independent scaling
Avoid premature decomposition when the team can’t yet operate distributed systems well
FHIR Gives Data a Shared Structure
FHIR matters because healthcare data loses value when systems interpret it differently. It provides a modern way to represent and exchange clinical information so applications can work with a more consistent data model.
A platform isn’t modern because it runs in the cloud. It’s modern when data can move with meaning intact.
FHIR doesn’t solve every integration problem on its own. Legacy data still needs mapping, governance, and validation. But without standards-based exchange, each new integration becomes a fresh negotiation between systems that speak different dialects.
The Stack Should Serve the Workflow
The strongest architecture decisions are tied to operational outcomes. If the technology doesn’t reduce admin effort, improve reliability, support secure exchange, or shorten the path to new services, it’s noise.
Modern stacks win because they let providers change one part of the platform without putting the whole organisation at risk.
Mastering Canadian Healthcare Compliance and Security
A hospital in Ontario replaces its patient portal, shifts reporting to the cloud, and adds a virtual care tool for rural outreach. Six months later, the project team realised the hard part was never the interface. It was proving where personal health information moved, which law applied at each step, and whether every vendor in the chain could support audits, retention, and breach response.
That is the Canadian reality. Compliance work starts before migration because architecture choices determine how much privacy risk, operational drag, and legal exposure you carry later.

PHIPA and PIPEDA Are Not Interchangeable
Canadian providers often hear PHIPA and PIPEDA mentioned in the same conversation and assume one checklist will cover both. It will not. PIPEDA is the federal private-sector privacy law. PHIPA governs personal health information in Ontario and applies directly to health information custodians and their agents. Other provinces have their own health privacy rules, and a multi-province delivery model can put different obligations on the same platform.
That has practical consequences during modernisation. Identity design, audit logging, consent workflows, data retention, third-party contracting, and breach procedures should be mapped to the actual jurisdictions, entities, and service arrangements involved.
Start with three decisions before any migration wave begins:
Map each dataset and workflow to the law that governs it
Document where data is stored, processed, backed up, and accessed
Assign accountability for tracing a record across vendors, interfaces, and internal teams
For teams building those controls into delivery, this guide to healthcare compliance software development is useful because privacy obligations show up in system design long before they appear in a policy binder.
Interoperability Failures Create Privacy Risk
In Canadian care delivery, interoperability is not only an efficiency problem. It is a compliance problem. Canada Health Infoway has long documented uneven digital maturity and fragmented information exchange across the country, especially between care settings and regions, which is one reason many providers still struggle to give clinicians complete, timely access to patient information (Canada Health Infoway).
The operational effect is familiar. Staff export files to bridge system gaps. Referral details get re-entered. Lab or imaging results are chased by phone or fax when interfaces fail. Every workaround creates another place where personal health information can be copied, misrouted, or left outside the audit trail.
This problem is sharper in rural Canada. Smaller hospitals and clinics often work with thinner IT coverage, older vendor contracts, and a limited budget for replacing core systems all at once. A modernisation plan that ignores those constraints usually increases risk instead of reducing it.
Why Phased Modernisation Usually Reduces Security Exposure
An abrupt replacement can look cleaner on a slide deck, but healthcare operations rarely behave that way. A phased model gives teams time to prove identity controls, audit coverage, data classification, and incident response on a smaller slice of the estate before expanding further.
That matters in Canada because cloud use, managed services, and cross-border tooling raise specific questions about data residency, subcontractors, and access by support teams outside the province or country. The Office of the Privacy Commissioner of Canada has been clear that organisations remain accountable for personal information transferred to third parties for processing, even when another service provider handles the infrastructure (OPC guidance on PIPEDA and processing).
In practice, the safer pattern is often hybrid. Keep high-risk workflows under tighter local control where needed. Modernise auditability, APIs, identity, and selected patient-facing services first. Retire old components in stages once the replacement controls work under real clinical load.
Security programs fail when clinicians need unofficial workarounds to do ordinary work.
What To Validate Before Procurement
Before approving a vendor, ask for evidence, not promises.
Audit design. Can the platform show who accessed a record, what changed, and which service or user account initiated the event?
Data residency and subcontractors. Where is data stored, where can it transit, and which downstream providers can touch it?
Integration governance. How are APIs authenticated, logged, monitored, and versioned over time?
AI oversight. If AI is included, how are prompts, outputs, human review, and retention handled?
Provincial fit. Can the product support province-specific privacy duties and the operational realities of urban and rural care settings?
Some organisations also use external research tools during vendor due diligence, especially when they need to review policy changes, supplier signals, or public digital footprints at scale. In that context, specialised web scraping capabilities can support procurement and compliance research workflows, provided they are used within your legal and governance boundaries.
For Canadian providers, modernisation and compliance are one operating decision. Separate them, and the project usually costs more, takes longer, and leaves more privacy debt behind.
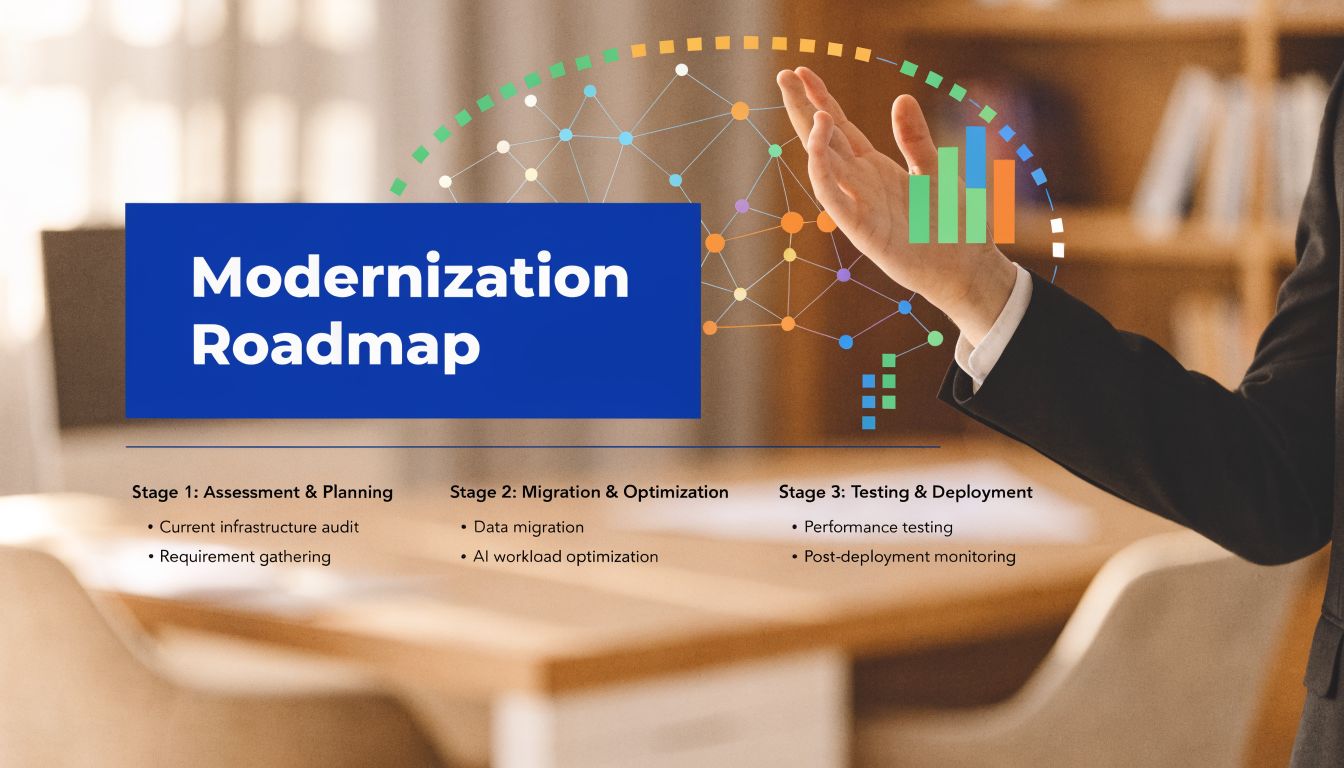
Your Step-by-Step Modernisation Implementation Roadmap
Most healthcare modernisation projects don’t fail because the technology is impossible. They fail because the sequence is wrong. Teams migrate before they simplify. They buy before they define requirements. They move data before they understand what should be retired, merged, or kept.
A workable roadmap keeps operations stable while reducing uncertainty at each stage.
Step One Is Discovery, Not Procurement
Start with an operational audit. List the systems in use, but don’t stop there. Map which workflows matter most, where duplicate entry happens, which reports are mission-critical, and which interfaces fail often enough that staff have built unofficial workarounds.
This phase should produce a small set of hard priorities. Examples include reducing intake friction, stabilising scheduling, improving referral flow, or making privacy auditing reliable.
Use a simple lens:
Keep what still supports care well
Fix what causes repeated operational pain
Retire what adds complexity without real value
Choose Scope Based on Risk, Not Enthusiasm
Once the current state is visible, choose a modernisation path that matches operational tolerance. In most healthcare environments, a phased programme is safer than a single cutover. Core clinical functions usually need a lower-risk path than peripheral systems.
A practical plan often separates work into streams such as infrastructure, integrations, patient-facing services, and data. That structure helps leadership see progress without forcing every dependency into one giant release.
Don’t start with the most visible feature. Start with the dependency that blocks five other improvements.
Implement in Controlled Phases
A good implementation roadmap usually follows this order:
Foundation work
Clean up identity, hosting, logging, environments, and integration governance first. These are invisible to patients, but they make everything after them safer.Low-disruption wins
Add or replace services that don’t destabilise the clinical core. Patient notifications, online forms, document workflows, or reporting layers often fit here.Core workflow transition
Move sensitive operational capabilities in small releases, with rollback paths and parallel validation where needed.Legacy retirement
Decommission only after usage, data integrity, and support ownership are clear.
Treat Data Migration As Its Own Workstream
Data migration is never just export and import. Records need mapping, validation, deduplication, archival rules, and access design. Historical data often contains structural inconsistencies that only show up when teams try to search, report, or audit across the new platform.
That’s why migration needs clinical, operational, and privacy input. An IT-only migration misses the meaning of the data. A clinician-only review misses the technical constraints.
Test Like a Care Organisation, Not a Software Lab
Healthcare testing has to reflect real workflows. It isn’t enough to confirm that forms submit or records load. You need to test appointment changes, consent handling, role-based access, downtime procedures, referrals, billing edge cases, and exception paths staff encounter.
Go-live should also be staged. Keep hypercare support close to end users. Track issues daily. Decide in advance which problems justify rollback and which can be fixed in place.
The smoothest projects feel almost uneventful to patients. That usually means the roadmap was disciplined.
Defining Success: Measuring KPIs and ROI
A hospital signs off on a modernisation budget, reaches go-live, and still cannot answer a basic board question six months later. What improved, by how much, and when did the organisation start seeing value? That gap usually comes from treating success as a technical milestone instead of an operating model change.
Healthcare platform modernisation services should be judged on outcomes that managers can defend. Faster intake. Fewer manual corrections. Better patient access. Lower support burden. Stronger auditability under PHIPA and PIPEDA. If those changes are not defined up front, the project can stay busy without becoming worthwhile.
Measure Before You Migrate
Start with the workflows that create the most friction today. Use a baseline that your clinic, hospital, or community care team can measure without building a new reporting project just to prove the first project worked.
Useful KPI groups usually include:
Patient access, such as online booking completion, portal adoption, no-show reduction, and turnaround time for routine requests
Administrative effort, including duplicate data entry, referral chasing, manual reconciliation, and time spent correcting incomplete records
Operational reliability, such as interface failures, ticket volume, recurring incidents, and recovery time after outages
Financial performance, including billing exceptions, rejected claims, delayed submissions, and staff hours tied up in rework
Adoption and change uptake, such as clinician usage by workflow, training completion, and support demand after go-live
Compliance performance, including audit log completeness, access review turnaround, and privacy incident response times
Pick a short list and keep it stable.
Too many teams track twenty indicators and manage none of them well. In practice, five to eight metrics tied to cost, access, and risk are usually enough to show whether the programme is working.
ROI in Rural Canada Needs a Different Lens
Canadian providers, especially smaller organisations outside major urban centres, often have to justify modernisation under tighter capital constraints, thinner IT coverage, and weaker vendor support than large health systems. The financial case also depends on local realities such as intermittent connectivity, shared regional services, and the cost of maintaining staff workarounds when a legacy platform keeps failing.
That is why ROI should be measured in phases, not only as a single end-state payback number. A rural clinic may not see a full return from interoperability or patient self-service in year one. It may still make the right investment if phase one cuts reception workload, reduces duplicate entry, and lowers the risk of privacy or downtime incidents that are expensive to manage in small teams.
Canada Health Infoway has documented ongoing gaps in digital health access and adoption across Canada, including differences that affect remote and underserved communities, which makes phased value measurement more realistic than a uniform benchmark for every provider (Canada Health Infoway). Separate reporting from the Canadian Institute for Health Information has also shown that rural access patterns and service delivery constraints differ materially from urban settings, which is why ROI models for Canadian modernisation work need local operating assumptions rather than imported US averages (Canadian Institute for Health Information).
What Tends To Hold Up in Board Review
A stronger business case usually starts with early operational wins and builds toward larger returns.
| KPI category | Early success signal | Longer-term outcome |
|---|---|---|
| Operations | Fewer manual workarounds and less duplicate handling | More consistent service delivery and lower interruption risk |
| Staff efficiency | Less time spent correcting records or chasing missing data | Lower administrative costs, and better staff retention |
| Patient service | Faster completion of routine tasks, and fewer phone handoffs | Better continuity, access, and patient satisfaction |
| Compliance and risk | Cleaner audit trails and faster access review | Lower privacy exposure and easier provincial reporting |
| Technology cost | Reduced support escalation, and fewer legacy fixes | Lower maintenance burden and clearer budgeting |
The trade-off is straightforward. A phased programme may show slower headline transformation than a full replacement plan, but it gives leadership earlier proof that each release improved cost, capacity, or risk. For many Canadian providers, especially those balancing provincial funding limits with day-to-day care delivery, that is the more credible ROI story.
If a programme needs several years before it can show one visible operational gain, the scope is usually too broad, or the release sequence is wrong.
Success in healthcare modernisation is not measured only by the final architecture. It is measured by whether each phase stands up to operational scrutiny, financial review, and Canadian compliance expectations on its own.
Partnering With Cleffex for Your Modernisation Journey
Healthcare modernisation in Canada is rarely blocked by a lack of intent. It’s blocked by competing realities. You need better systems, but you also need continuity of care. You want cloud flexibility, but you also need privacy controls that match Canadian requirements. You need interoperability improvements, but you can’t afford a migration approach that overwhelms staff or stalls halfway through.
That’s where a delivery partner matters. Not as a software seller, but as a team that can translate business pressure into a practical rollout plan.
For organisations evaluating vendors, one option is Cleffex Digital Ltd, which supports custom software development, cloud modernisation, and healthcare-focused delivery for teams that need phased change rather than a single disruptive replacement. In practice, that means aligning architecture, security, and release planning with the way a clinic network or hospital group operates.
Consider a common Ontario scenario. A medium-sized clinic network has legacy scheduling, limited patient self-service, inconsistent data exchange between systems, and compliance concerns around cloud migration. The sensible path usually isn’t a full rip-and-replace. It’s a staged programme: stabilise integrations, modernise selected workflows, improve auditing, and retire older components when the replacement path is proven.
That kind of approach tends to work better because it respects the two things healthcare organisations can’t compromise on. Daily operations and trust.
If you’re planning your first major overhaul, ask sharper questions before you sign anything. Which workflows must remain untouched at first? Which systems create the most rework? Which privacy obligations shape architecture choices? Which phase can prove value early enough to sustain internal support?
A good modernisation partner should be able to answer those questions in plain language, with a roadmap your operations team can live with.
If your organisation is weighing healthcare platform modernisation services and needs a Canadian-first plan that reflects compliance, interoperability, and budget realities, book a conversation with Cleffex Digital Ltd. A focused assessment can help you identify the safest starting point, the right modernisation pattern, and the fastest path to measurable operational improvement.







